Cloud Computing Patterns, Mechanisms > Mechanisms > C > Cryptographic Key Management System
Cryptographic Key Management System

The cryptographic key management system (CKMS) consists of policies, procedures, components and devices that are used to protect, manage, and distribute cryptographic keys and certain specific information, called metadata. A CKMS includes all devices or sub-systems that can access an unencrypted key or its metadata. Encrypted keys and their cryptographically protected metadata can be handled by computers and transmitted through communications systems and stored in media that are not considered to be part of a CKMS.
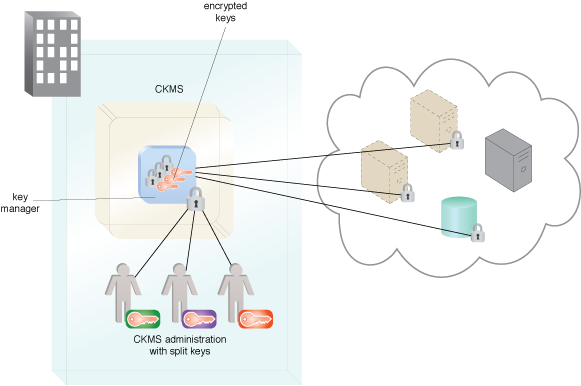
Figure 1 – An example of a CKMS using split key administration.
Figure 1 shows a CKMS managing the organization’s keys. Many industry regulations require organizations to control their own keys, which can be done on-premise or from a trusted third-party service. It shows the requirement for multiple administrators to accomplish management tasks requiring multiple split keys to perform a cryptographic operation.
Related Patterns:
- Cloud Data Breach Protection
- Cloud Key Management
- Cloud Storage Data at Rest Encryption
- Cloud Storage Device Masking
- Cloud Traffic Hijacking Protection
- Cloud VM Platform Encryption
- In-Transit Cloud Data Encryption
- Permanent Data Loss Protection
This mechanism is covered in CCP Module 7: Fundamental Cloud Security and
in Module 8: Advanced Cloud Security.
For more information regarding the Cloud Certified Professional (CCP) curriculum, visit www.arcitura.com/ccp.
This cloud computing mechanism is also covered in:
Cloud Computing Design Patterns by Thomas Erl, Robert Cope, Amin Naserpour
(ISBN: 9780133858563, Hardcover, ~ 528 pages)
For more information about this book, visit www.arcitura.com/books.


