Cloud Computing Patterns, Mechanisms > Virtual Server and Hypervisor Connectivity and Management Patterns > Virtual Server-to-Host Connectivity
Virtual Server-to-Host Connectivity (Erl, Naserpour)
How can a virtual server and hypervisor communicate with one another securely without impacting other communication within the network?

Problem
A virtual server needs to have its communication restricted to only its host hypervisor, without affecting or having access to any other network communication.
Solution
A secure network-based channel of communication between the virtual server and hypervisor needs to be created.
Application
A new virtual switch is introduced, configured specifically to support this mode of communication.
Mechanisms
Compound Patterns
Burst In, Burst Out to Private Cloud, Burst Out to Public Cloud, Cloud Authentication, Cloud Balancing, Elastic Environment, Infrastructure-as-a-Service (IaaS), Isolated Trust Boundary, Multitenant Environment, Platform-as-a-Service (PaaS), Private Cloud, Public Cloud, Resilient Environment, Resource Workload Management, Secure Burst Out to Private Cloud/Public Cloud, Software-as-a-Service (SaaS)
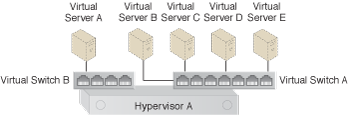
Virtual Switch B is configured to limit Virtual Server A’s connectivity to the hypervisor only, which prevents Virtual Switch B from sending any of Virtual Server A’s traffic to or from the network.
This pattern is covered in CCP Module 17: Advanced Cloud Virtualization.
For more information regarding the Cloud Certified Professional (CCP) curriculum, visit www.arcitura.com/ccp.