Cloud Computing Patterns, Mechanisms > Mechanisms > A - B > Audit Monitor
Audit Monitor
The audit monitor mechanism is used to collect audit tracking data for networks and IT resources in support of, or dictated by, regulatory and contractual obligations. The figure depicts an audit monitor implemented as a monitoring agent that intercepts “login” requests and stores the requestor’s security credentials, as well as both failed and successful login attempts, in a log database for future audit reporting purposes.
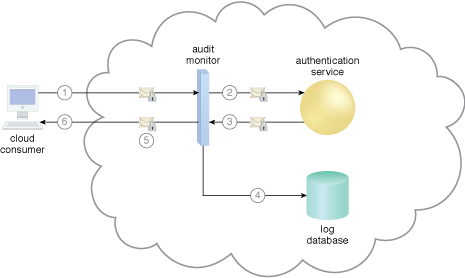
A cloud service consumer requests access to a cloud service by sending a login request message with security credentials (1). The audit monitor intercepts the message (2) and forwards it to the authentication service (3). The authentication service processes the security credentials. A response message is generated for the cloud service consumer, in addition to the results from the login attempt (4). The audit monitor intercepts the response message and stores the entire collected login event details in the log database, as per the organization’s audit policy requirements (5). Access has been granted, and a response is sent back to the cloud service consumer (6).
Related Patterns:
- Centralized Remote Administration
- Container Chain
- Cross-Storage Device Vertical Tiering
- Dynamic Failure Detection and Recovery
- Multi-Container Isolation Control
- Realtime Resource Availability
- Resource Management
- Resource Pooling
- Resource Reservation
- Self-Provisioning
- Shared Resources
- Storage Workload Management
- Usage Monitoring
- Workload Distribution
- Zero Downtime
This mechanism is covered in CCP Module 4: Fundamental Cloud Architecture.
For more information regarding the Cloud Certified Professional (CCP) curriculum, visit www.arcitura.com/ccp.
This cloud computing mechanism is covered in:
Cloud Computing: Concepts, Technology & Architecture by Thomas Erl, Zaigham Mahmood,
Ricardo Puttini
(ISBN: 9780133387520, Hardcover, 260+ Illustrations, 528 pages)
For more information about this book, visit www.arcitura.com/books.

