Cloud Computing Patterns, Mechanisms > Monitoring, Provisioning and Administration Patterns > Automated Administration
Automated Administration (Erl, Naserpour)
How can common administrative tasks be carried out consistently and automatically in response to pre-defined events?

Problem
IT resources undergo numerous administrative tasks that need to be repeatedly and efficiently carried out and become subject to human error and slow response times when performed manually.
Solution
The workflow logic of administration tasks suitable for automation is programmed using scripts and deployed in a platform capable of executing these scripts in response to pre-defined runtime events.
Application
An intelligent automation engine is implemented to establish a system capable of storing, managing and executing the automation scripts.
Mechanisms
Automated Scaling Listener, Cloud Storage Device, Cloud Usage Monitor, Container, Hypervisor, Resource Replication, Virtual Server
Compound Patterns
Burst In, Burst Out to Private Cloud, Burst Out to Public Cloud, Cloud Authentication, Cloud Balancing, Elastic Environment, Infrastructure-as-a-Service (IaaS), Isolated Trust Boundary, Multitenant Environment, Platform-as-a-Service (PaaS), Private Cloud, Public Cloud, Resilient Environment, Resource Workload Management, Secure Burst Out to Private Cloud/Public Cloud, Software-as-a-Service (SaaS)
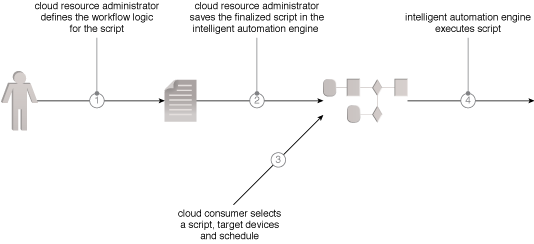 The cloud resource administrator defines the workflow logic (1) and expresses it in a series of scripts that is incorporated into an intelligent automation engine repository (2). The cloud resource administrator then selects the workflow, the systems it will run on, and its execution schedule (3). The intelligent automation engine runs the workflow and reports the results (4).
The cloud resource administrator defines the workflow logic (1) and expresses it in a series of scripts that is incorporated into an intelligent automation engine repository (2). The cloud resource administrator then selects the workflow, the systems it will run on, and its execution schedule (3). The intelligent automation engine runs the workflow and reports the results (4).
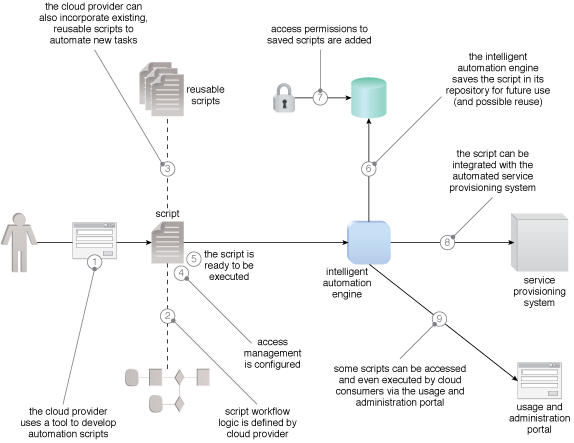 An overview of how the components can be assembled as a result of the application of this pattern.
An overview of how the components can be assembled as a result of the application of this pattern.
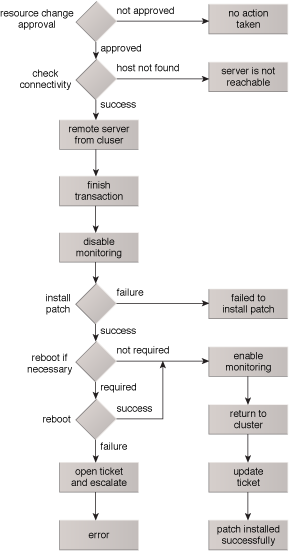 This scenario depicts a physical server that needs patching, which is a routine task and a prime candidate for automation. The physical server is part of a cluster, so the script needs to ensure that the physical server is properly taken offline and monitoring is disabled before initiating the patching process.
This scenario depicts a physical server that needs patching, which is a routine task and a prime candidate for automation. The physical server is part of a cluster, so the script needs to ensure that the physical server is properly taken offline and monitoring is disabled before initiating the patching process.
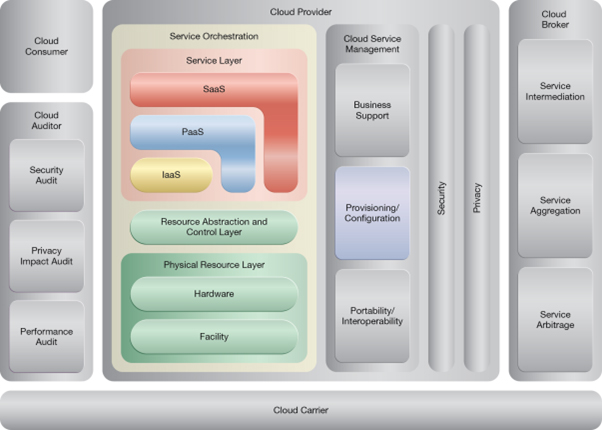
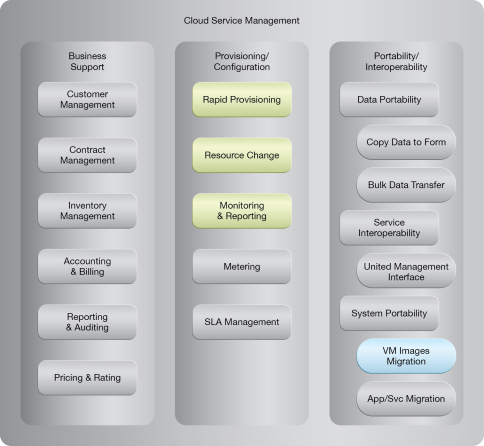
NIST Reference Architecture Mapping
This pattern relates to the highlighted parts of the NIST reference architecture, as follows:
This pattern is covered in CCP Module 4: Fundamental Cloud Architecture.
For more information regarding the Cloud Certified Professional (CCP) curriculum, visit www.arcitura.com/ccp.
