Cloud Computing Patterns, Mechanisms > Cloud Service and Storage Security Patterns > Trusted Platform BIOS
Trusted Platform BIOS (Cope, Erl)
How can the BIOS on a cloud-based environment be protected from malicious code?

Problem
Malware and rootkits can start before the operating system is launched, completely bypassing operating system security and remaining completely hidden.
Solution
Using security validation from the silicon up and remote monitoring of the platform security status, cloud consumers can verify that they are using compute platforms that meet their security assurance requirements.
Application
Trusted compute platforms are made available by the cloud provider with trusted platform modules (TPMs) which are hardware security modules (HSMs) that enable security assurance by validating digital signatures of code, starting at the basic input/output system (BIOS) using a measured boot.
Compound Patterns
Burst In, Burst Out to Private Cloud, Burst Out to Public Cloud, Cloud Authentication, Cloud Balancing, Elastic Environment, Infrastructure-as-a-Service (IaaS), Isolated Trust Boundary, Multitenant Environment, Platform-as-a-Service (PaaS), Private Cloud, Public Cloud, Resilient Environment, Resource Workload Management, Secure Burst Out to Private Cloud/Public Cloud, Software-as-a-Service (SaaS)
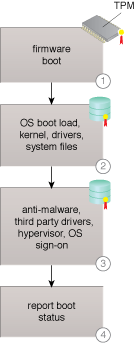
A platform startup sequence with a trusted BIOS.
This mechanism is covered in CCP Module 7: Fundamental Cloud Security and
in Module 8: Advanced Cloud Security.
For more information regarding the Cloud Certified Professional (CCP) curriculum, visit www.arcitura.com/ccp.
The architectural model upon which this design pattern is based is further covered in:
Cloud Computing Design Patterns by Thomas Erl, Robert Cope, Amin Naserpour
(ISBN: 9780133858563, Hardcover, ~ 528 pages)
For more information about this book, visit www.arcitura.com/books.


