Cloud Computing Patterns, Mechanisms > Mechanisms > R - S > Single Sign-On
Single Sign-On

Propagating the authentication and authorization information for a cloud service consumer across multiple cloud services can be a challenge, especially if multiple cloud services or cloud-based IT resources need to be invoked as part of the same overall runtime activity. The single sign-on (SSO) mechanism enables one cloud service consumer to be authenticated by a security broker, which establishes a security context that is persisted while the cloud service consumer accesses other cloud services or cloud-based IT resources. Otherwise, the service consumer would need to re-authenticate itself with every subsequent request.
An advantage to the SSO mechanism is how it enables mutually independent services and IT resources to generate and circulate runtime authentication and authorization credentials. The credentials initially provided by the cloud consumer remain valid for the duration of the user’s session, while its security context information is shared with the other IT resources. The SSO mechanism’s security broker is especially useful when a cloud consumer needs to access cloud services residing on different clouds (Figure 1).
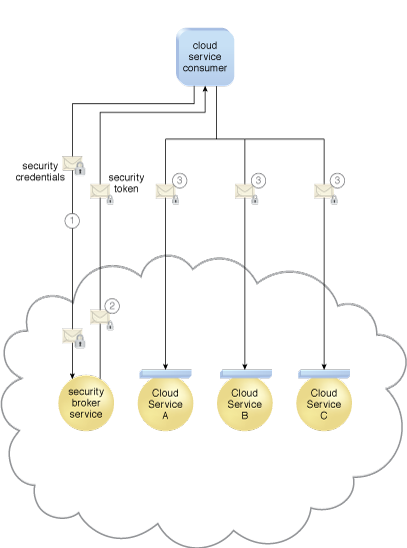
Figure 1 – A cloud service consumer provides the security broker with login credentials (1). The security broker responds with an authentication token (message with small lock symbol) upon successful authentication, which contains cloud service consumer identity information (2) that is used to automatically authenticate the cloud service consumer by Cloud Services A, B, and C (3).
Related Patterns:
This mechanism is covered in CCP Module 7: Fundamental Cloud Security and
in Module 8: Advanced Cloud Security.
For more information regarding the Cloud Certified Professional (CCP) curriculum, visit www.arcitura.com/ccp.
The architectural model upon which this design pattern is based is further covered in:
Cloud Computing Design Patterns by Thomas Erl, Robert Cope, Amin Naserpour
(ISBN: 9780133858563, Hardcover, ~ 528 pages)
For more information about this book, visit www.arcitura.com/books.


