SOA Patterns > Service Security Patterns > Exception Shielding
Exception Shielding (Hogg, Smith, Chong, Hollander, Kozaczynski, Brader, Delgado, Taylor, Wall, Slater, Imran, Cibraro, Cunningham)
How can a service prevent the disclosure of information about its internal implementation when an exception occurs?

Problem
Unfiltered exception data output by a service may contain internal implementation details that can compromise the security of the service and its surrounding environment.
Solution
Potentially unsafe exception data is “sanitized” by replacing it with exception data that is safe by design before it is made available to consumers.
Application
This pattern can be applied at design time by reviewing and altering source code or at runtime by adding dynamic sanitization routines.
Impacts
Sanitized exception information can make the tracking of errors more difficult due to the lack of detail provided to consumers.
Principles
Architecture
Service
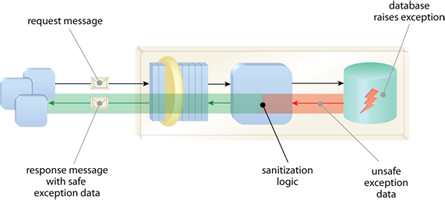
Potentially unsafe information is sanitized by routines added to the service logic, thereby releasing only safe exception information to service consumers.
Related Patterns in This Catalog
Service Agent, Service Perimeter Guard, Utility Abstraction
Related Service-Oriented Computing Goals
This pattern is covered in SOACP Module 19: Advanced Security for Services, Microservices & SOA.
For more information regarding the SOA Certified Pofessional (SOACP) curriculum,
visit www.arcitura.com/soa.
This page contains excerpts from:
SOA Design Patterns by Thomas Erl
(ISBN: 0136135161, Hardcover, Full-Color, 400+ Illustrations, 865 pages)
For more information about this book, visit www.arcitura.com/books.

